EFA XDS ResourceManager
Dieses Material ist Teil des Leitfadens CDA für die elektronische Fallakte.
|
Anmerkung: Die Kürzel unter den einzelnen Überschriften dienen der Unterstützung des Kommentierungsverfahrens. Bitte geben Sie bei einem Kommentar oder einem Verbesserungsvorschlag zu dieser Spezifikation immer das Kürzel des Abschnitts an, auf den sich Ihr Kommentar bezieht. Alle Kommentare werden in der Lasche "Diskussion" zu der kommentierten Seite gesammelt und gegenkommentiert.
Hinweise zum Kommentierungsverfahren einschließlich aller Formulare und Kontaktadressen finden Sie auf der Seite "Kommentierung EFAv2.0".
Inhaltsverzeichnis
- 1 EFA Resource Manager XDR/XDS Binding
- 2 EFA XDS/XDR Binding: createECR
- 3 EFA XDS/XDR Binding: createPartition
- 4 EFA XDS/XDR Binding: closeECR
- 5 EFA XDS Binding: listPartitions
- 6 EFA XDS/XDR Binding: registerConsent
- 7 EFA IHE-ITI-Binding: listRecordLocations
- 8 EFA IHE-ITI-Binding: registerRecordLocation
- 9 EFA IHE-ITI-Binding: notifyOfConsent
- 10 Referenzen und Querverweise
EFA Resource Manager XDR/XDS Binding
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.01}
Within EFA the actors and transactions of the IHE XDS integration profile are mapped onto EFA Resource Manager actors and operations as follows:
| Role | EFA Resource Manager Service | IHE XDS | Binding |
|---|---|---|---|
| Actor | EFA Consumer |
|
- |
| Actor | EFA Resource Manager |
|
- |
| Transaction | createECR | Provide and Register Document Set ITI-41 | createECR |
| Transaction | createPartition | Provide and Register Document Set ITI-41 | createPartition |
| Transaction | closeECR | Provide and Register Document Set ITI-41 | closeECR |
| Transaction | listPartitions | Registry Stored Query ITI-18 | listPartitions |
| Transaction | registerConsent | Provide and Register Document Set ITI-41 | registerConsent |
| Transaction | listRecordLocations | Patient Location Query ITI-56 | |
| Transaction | registerRecordLocation | Patient Identity Feed HL7 V3 ITI-44 | |
| Transaction | notifyOfConsent | Document Metadata Notify ITI-53 |
EFA XDS/XDR Binding: createECR
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.02}
The initialization of a new ECR is performed by creating a new XDS folder for the patient. The folder is classified by the ECR purpose codes and as such implicitly linked to all other folders (ECR: partitions) which are assigned to the same purpose.
This EFA binding introduces the following extensions and restrictions on the IHE XDR actor and transaction definitions in order to properly cover the EFA createECR operation and to align with the EFA security framework:
- A new folder shall be created and purpose codes shall be provided for the newly created folder as codeList.
- A consent information document containing the list of authorized subjects shall be provided through BPPC. A scanned consent document may be additionaly provided.
- Additional error messages are defined that cover specific failure conditions of the EFA use cases
- The availability of data fields is aligned to EFA privacy requirements
- The application of security measures and the contents of the SOAP security header are specified normatively
Constraints on the Request Message
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.02.01}
The createECR request message implements the IHE Provide And Register DocumentSet transaction (ITI-41) request message as profiled in [IHE ITI TF-2b]
The following table shows how the createECR Service Functional Model is mapped onto the ITI-41 transaction:
| createECR | ITI-41 | Constraints | |
|---|---|---|---|
| context | SAML Identity Assertion within the SOAP Security Header | see IHE Cookbook | |
| ecrInfo | patientID | XDS Folder Attribute: patientID XDS Document Attribute: patientID |
The same patient identifier SHALL be used throughout all metadata |
| purpose | XDS Folder Attribute: codeList | see EFA XDS Folder Metadata Binding for details | |
| ecrStatus | XDS Folder Attribute: availabilityStatus | SHALL be "approved". | |
| consentInfo | XDS Document | ||
| consentDoc (optional) | XDS Document | Scaned documents SHALL be provided acc. to the XDS SD Integration Profile. | |
Following this, implementations SHALL satisfy
- the Common constraints on ITI-41,
- the distinct set of constraints which trigger this binding, given in the table below (R = required, O = optional, - = forbidden).
| Constraints | createECR binding |
|---|---|
| One XDS Document is a consentInfo which gives a new consent or does not revoke all active consents | R |
| One XDS Document is a consentInfo, which revokes all active consents | - |
| The provided XDS Folder and a registered XDS Folder have the XDSFolder.codeList and XDSFolder.patientID in common (i.e. the EFA exists) | - |
| The XDS Folder is not registered (uniqueID) | R |
| The XDSFolder is registered (uniqueID) | - |
Expected Actions
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.02.02}
The XDS Document Repository SHALL respond to an ProvideAndRegisterDocument request message with the ProvideAndRegisterDocument response message containing a success indicator.
The XDS Document Repository MUST verify that the requesting service user has sufficient rights to setup a new ECR at this EFA Provider. This includes that the service user is registered with the provider and familiar with using ECRs. Additionaly the EFA Provider SHALL verify the completeness and consistency of the provided consentInfo document. It SHALL verify that all named ECR participants are either registered with the provider or identifiable through a shared healthcare provider directory.
The EFA Provider SHALL check if an ECR for the given patient and purpose already has been registered with this provider.
If no ECR with the given purpose exists for the given patient, the EFA Provider SHALL
- setup a folder as specified in the request message
- translate the provided consentInfo document into an access control policy which can be automatically enforced for each request to the newly setup ECR
- store the provided documents within the XDS Document Repository
- forward the metadata of the received documents to the XDS Document Registry for registration
If an ECR with the given purpose already exists for the given patient, the EFA Provider SHALL
- verify that EFA participant is allowed to modify the consent of the ECR. If this access is denied an error status SHALL be returned.
- setup a folder as specified in the request message
- extract the identified ECR participants from the provided consentInfo document and add them as authorized users to the existing access control policy.
- store the provided documents within the XDS Document Repository
- forward the metadata of the received documents to the XDS Document Registry for registration
In case of an error that relates to the transmission of the request or the processing of the EFA security token, the EFA Resource Manager MUST respond with the respective error status.
Response Message (Full Success Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.02.03}
If the XDS Document Registry is able to decode the received message and to properly initialize the new ECR and its initial partition it responds with an ebXML Registry Response with its status set to "urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Success"
If the XDS Document Registry wants to respond with further information on the processing of the transmitted data or with a non-critical warning it SHOULD include an additional <RegistryErrorList> element. The severity MUST be set to “urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Warning”:
<rs:RegistryResponse
status="urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Success">
<rs:RegistryErrorList>
<rs:RegistryError
severity=”urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Warning”
errorCode=”....”
codeContext=”Partition linked with existing ECR”
location="" />
</rs:RegistryErrorList>
</rs:RegistryResponse>
The following warning messages and codes are defined:
| Condition and Severity | Message | Code | Action to be taken |
|---|---|---|---|
| Request was received but not processed; e.g. because a manual intervention by the EFA Provider is required to initalize a new ECR | Processing deferred | 2201 | None |
| An ECR with the given purpose already exists for the patient. Instead of initalizing a new ECR a partition has been added to the existing ECR. | Partition linked with existing ECR | 2202 | None |
Response Message (Failure or Partial Failure Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.02.04}
If the XDS Document Repository is able to decode the received message but the processing of the request failed, it responds with an ebXML Registry Response that contains a respective status indicator (see below).The response MUST contain a RegistryErrorList element that indicates the failure condition.
The instantiation of an ECR is an All-or-Nothing operation. Therefore in any case of failure the response status MUST be set to “urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Failure”.
The severity of each registry error message MUST be set to ”urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Error”. Multiple registry error messages MAY be included within a single <rs:RegistryErrorList> element. Apart from the XDS-b error messages defined in Table 4.1-11 of [IHE ITI TF-3] the following error codes are defined for EFA:
| Condition and Severity | Location | Message | Code | Action to be taken |
|---|---|---|---|---|
| The EFA provider requests a higher authentication trust level than assigned to the HP (e.g. password-based login is not accepted for the requested operation). (ERROR) | - | Weak Authentication | 4702 | If possible, the HP SHOULD log in again with a stronger mechansims (e.g. smartcard) and re-issue the request with the respective identity assertion. |
| The EFA Provider only accepts consentInfo documents if they are digitally signed by an HP. (ERROR) | OID of the consentInfo document | No Signature | 4704 | If possible, the EFA Client SHOULD re-issue the request with the data signed by an HP. |
| The requestor has not sufficient permission to perform the requested operation (ERROR) | - | No Consent | 4701 | The request MUST NOT be processed by the service provider. The HP MAY request the patient to extend the consent. |
| An ECR of the given purpose already exists for the patient. The requestor does not have sufficient permissions to create a new partiton and to register new participants (ERROR) | - | No Consent | 4701 | The request MUST NOT be processed by the service provider. The HP MAY request the patient to extend the consent for the existing ECR. |
| The EFA Provider is unable to identify one or more of the participants that are listed in the consentInfo document (ERROR) | OID of the participant that cannot be identified | Unknown HP Identity | 4111 | The request MUST NOT be processed by the service provider. The requestor SHOULD first resolve the participants' identities into identifiers which are resolvable to the EFA Provider. |
Security Considerations
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.02.05}
Message Protection
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.02.05.01}
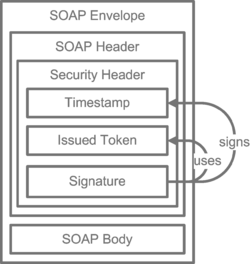
The ECR requester MUST apply means to achieve message authenticity, message integrity and message confidentiality. The EFA Resource Manager MUST approve at least one of the following mechanisms.
Transport Layer Security with SAML Issued Endorsing Token
The request message and the response message are sent over an EFA Resource Manager authenticated TLS-channel. In the SOAP Security Header the EFA client provides an EFA Identity Assertion and a wsu:timestamp element. If the SAML subject confirmation method is set to holder-of-key the wsu:timestamp element MUST be signed with the Subject-Confirmation-Key. If the SAML subject confirmation method is set to bearer the TLS-channel MUST be mutually authenticated.
WS-Security-Policy Example
<wsp:Policy wsu:Id="ServicePortBindingPolicy">
<sp:TransportBinding>
<wsp:Policy>
<sp:TransportToken>
<wsp:Policy>
<sp:HttpsToken RequireClientCertificate="false" />
</wsp:Policy>
</sp:TransportToken>
<sp:AlgorithmSuite>
<wsp:Policy>
<sp:Basic256Sha256 />
</wsp:Policy>
</sp:AlgorithmSuite>
<sp:IncludeTimestamp />
<sp:Layout>
<wsp:Policy>
<sp:Strict />
</wsp:Policy>
</sp:Layout>
</wsp:Policy>
</sp:TransportBinding>
<sp:Wss11>
<wsp:Policy />
</sp:Wss11>
<wsam:Addressing />
</wsp:Policy>
<wsp:Policy wsu:Id="Input_Policy">
<sp:EndorsingSupportingTokens>
<wsp:Policy>
<sp:IssuedToken
sp:IncludeToken="http://schemas.xmlsoap.org/ws/2005/07/securitypolicy/IncludeTokenAlwaysToRecipient">
<sp:RequestSecurityTokenTemplate>
<wst:TokenType>http://docs.oasis-open.org/wss/oasis-wss-saml-token-profile-1.1#SAMLV2.0</wst:TokenType>
<wst:KeySize>2048</wst:KeySize>
</sp:RequestSecurityTokenTemplate>
<wsp:Policy></wsp:Policy>
</sp:IssuedToken>
</wsp:Policy>
</sp:EndorsingSupportingTokens>
</wsp:Policy>
Asymmetric Message Protection
The request message and the response message are signed and encrypted. The ECR requester uses the key material corresponding with the Subject-Confirmation-Key provided with the issued EFA Identity Assertion. The EFA Provider uses its service certificate and key. The wsu:timestamp element, all WS-Addressing elements and the SOAP-Body element MUST be signed. The SOAP-Body element MUST be encrypted.
WS-Security-Policy Example
<wsp:Policy wsu:Id="ServicePortBindingPolicy">
<sp:AsymmetricBinding>
<wsp:Policy>
<sp:InitiatorToken>
<wsp:Policy>
<sp:IssuedToken sp:IncludeToken="http://schemas.xmlsoap.org/ws/2005/07/securitypolicy/IncludeToken/AlwaysToRecipient">
<sp:RequestSecurityTokenTemplate>
<wst:TokenType>http://docs.oasis-open.org/wss/oasis-wss-saml-token-profile-1.1#SAMLV2.0</wst:TokenType>
<wst:KeySize>2048</wst:KeySize>
</sp:RequestSecurityTokenTemplate>
<wsp:Policy></wsp:Policy>
</sp:IssuedToken>
</wsp:Policy>
</sp:InitiatorToken>
<sp:RecipientToken>
<wsp:Policy>
<sp:X509Token sp:IncludeToken="http://schemas.xmlsoap.org/ws/2005/07/securitypolicy/IncludeToken/AlwaysToInitiator">
<wsp:Policy><sp:WssX509V3Token10 /></wsp:Policy>
</sp:X509Token>
</wsp:Policy>
</sp:RecipientToken>
<sp:AlgorithmSuite><wsp:Policy><sp:Basic256 /></wsp:Policy></sp:AlgorithmSuite>
<sp:Layout><wsp:Policy><sp:Strict /></wsp:Policy></sp:Layout>
<sp:IncludeTimestamp />
<sp:OnlySignEntireHeadersAndBody />
</wsp:Policy>
</sp:AsymmetricBinding>
<sp:Wss11><wsp:Policy></wsp:Policy></sp:Wss11>
<sp:Trust10>
<wsp:Policy><sp:MustSupportIssuedTokens /></wsp:Policy>
</sp:Trust10>
<wsap10:UsingAddressing />
</wsp:Policy>
WS-SecureConversation bootstrapped with SAML Issued Token
The request message and the response message are signed and encrypted. Both the ECR requester and the EFA Provider use a symmetric Secure-Conversation-Token key. The Secure-Conversation-Token MUST reference the issued EFA Identity Assertion. The wsu:timestamp element, all WS-Addressing elements and the SOAP-Body element MUST be signed. The SOAP-Body element MUST be encrypted.
Audit Trail
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.02.05.02}
Service consumer and service provider actors SHALL write an audit trail according to the EFAv2 Audit Trail Binding.
EFA XDS/XDR Binding: createPartition
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.03}
The linkage of a new partition to an existing ECR is performed by creating a new XDS folder for the patient. The folder is classified by the ECR purpose codes of the existing ECR and as such implicitly linked to all other folders (ECR: partitions) which are already assigned to the same ECR.
This EFA binding introduces the following extensions and restrictions on the IHE XDR actor and transaction definitions in order to properly cover the EFA createPartition operation and to align with the EFA security framework:
- A new folder shall be created and purpose codes shall be provided for the newly created folder as codeList
- Additional error messages are defined that cover specific failure conditions of the EFA use cases
- The availability of data fields is aligned to EFA privacy requirements
- The application of security measures and the contents of the SOAP security header are specified normatively
Constraints on the Request Message
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.03.01}
The createPartition request message implements the IHE Provide And Register DocumentSet transaction (ITI-41) request message as profiled in [IHE ITI TF-2b]
The following table shows how the createPartition SFM is mapped onto the ITI-41 transaction:
| createPartition | ITI-41 | Constraints |
|---|---|---|
| context | SAML Identity Assertion within the SOAP Security Header | see IHE Cookbook |
| ecrRef |
XDS Folder Attribute: patientID |
The codeList shall contain all purpose codes as assigned to the existing ECR the new partition is to be linked with |
| partitionInfo | XDS Folder Attribute: title XDS Folder Attribute: uniqueID |
Further elements of the partitionInfo structure MAY be set by the ECR provider. |
| initialDoc | XDS Document | At least a single document shall be provided when a new partition is initialized. |
Following this, implementations SHALL satisfy
- the Common constraints on ITI-41,
- the distinct set of constraints which trigger this binding, given in the table below (R = required, O = optional, - = forbidden).
| Constraints | createPartition binding |
|---|---|
| One XDS Document is a consentInfo which gives a new consent or does not revoke all active consents | - |
| One XDS Document is a consentInfo, which revokes all active consents | - |
| The provided XDS Folder and a registered XDS Folder have the XDSFolder.codeList and XDSFolder.patientID in common (i.e. the EFA exists) | R |
| The XDS Folder is not registered (uniqueID) | R |
| The XDSFolder is registered (uniqueID) | - |
Expected Actions
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.03.02}
The XDS Document Repository provider SHALL respond to an ProvideAndRegisterDocument request message with the ProvideAndRegisterDocument response message containing a success indicator.
The provider of the XDS Document Repository provider MUST verify that the requesting service user has sufficient rights to setup a new partition at this ECR Provider ant to link this partiton with an existing ECR.
In processing of this request the ECR Provider SHALL
- assess the access control policy of the ECR with the "create partition" operation
- setup a folder as specified in the request message
- store the provided documents within the XDR Document Repository
- forward the metadata of the received documents to the XDS Document Registry for registration
In case of an error that relates to the transmission of the request or the processing of the EFA security token, the XDS Document Repository MUST respond with the respective error status.
Response Message (Full Success Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.03.03}
If the EFA Document Registry Service provider is able to decode the received message and to properly initialize the new partition it responds with an ebXML Registry Response with its status set to "urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Success"
Response Message (Failure or Partial Failure Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.03.04}
If the XDS Document Repository is able to decode the received message but the processing of the request failed, it responds with an ebXML Registry Response that contains a respective status indicator (see below).The response MUST contain a RegistryErrorList element that indicates the failure condition.
If the partiton could not be created or if none of the provided documents was processed succesfully, the response status MUST be set to “urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Failure”. If the partition was successfully initialized and at least one document was processed successfully, the response status MUST be set to “urn:ihe:iti:2007:ResponseStatusType:PartialSuccess”. A failure location MUST be provided if the error does not apply to all provided documents. It MUST NOT be given if the error applies to all provided documents.
The severity of each registry error message MUST be set to ”urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Error”. Multiple registry error messages MAY be included within a single <rs:RegistryErrorList> element. Apart from the XDS-b error messages defined in Table 4.1-11 of [IHE ITI TF-3] the following error codes are defined for EFA:
| Condition and Severity | Location | Message | Code | Action to be taken |
|---|---|---|---|---|
| The EFA provider requests a higher authentication trust level than assigned to the HP (e.g. password-based login is not accepted for the requested operation). (ERROR) | - | Weak Authentication | 4702 | If possible, the HP SHOULD log in again with a stronger mechansims (e.g. smartcard) and re-issue the request with the respective identity assertion. |
| An ECR of the given purpose does not exist for the patient (ERROR) | - | Policy Violation | 4109 | The request MUST NOT be processed by the service provider. |
| The ECR provider only accepts medical documents if they are digitally signed by an HP. (ERROR) | OID of the consentInfo document | No Signature | 4704 | If possible, the EFA Client SHOULD re-issue the request with the data signed by an HP. |
| The requestor has not sufficient permission to perform the requested operation (ERROR) | - | No Consent | 4701 | The request MUST NOT be processed by the service provider. The HP MAY request the patient to extend the consent. |
| For data of the given kind the EFA provider only accepts PDF coded documents (ERROR) | OID of the document | PDF required | 4107 | The provided document MUST NOT be processed by the EFA provider. The EFA Client MUST re-transmit the document in PDF format. |
| A document of the provided kind does not comply with the EFA policy or the patient consent (ERROR) | OID of the document | No Consent | 4701 | The provided document MUST NOT be processed by the service provider. The HP MAY request the patient to extend the consent. |
Security Considerations
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.03.05}
Message Protection
See Message Protection topic in createECR section.
Audit Trail
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.03.05.02}
Service consumer and service provider actors SHALL write an audit trail according to the EFAv2 Audit Trail Binding.
EFA XDS/XDR Binding: closeECR
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.04}
The explicit shutdown of an ECR is performed by placing a consentInfo document that invalidates all previously given permissions into one of the ECR's partitions (folders). This may either be a newly created folder of an existing folder that is classified by the ECR purpose codes and as such implicitly represents the ECR that is to be closed.
This EFA binding introduces the following extensions and restrictions on the IHE XDR actor and transaction definitions in order to properly cover the EFA closeECR operation and to align with the EFA security framework:
- A new folder may be created. Purpose codes shall be provided for the newly created folder as codeList
- A consent information document that invalidates all previously given permissions shall be provided through BPPC. A scanned consent revocation document may be additionaly provided.
- Additional error messages are defined that cover specific failure conditions of the EFA use cases
- The availability of data fields is aligned to EFA privacy requirements
- The application of security measures and the contents of the SOAP security header are specified normatively
Constraints on the Request Message
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.04.01}
The closeECR request message implements the IHE Provide And Register DocumentSet transaction (ITI-41) request message as profiled in [IHE ITI TF-2b]
The following table shows how the closeECR SFM is mapped onto the ITI-41 transaction:
| closeECR | ITI-41 | Constraints |
|---|---|---|
| context | SAML Identity Assertion within the SOAP Security Header | see IHE Cookbook |
| ecrRef | XDS Folder Attribute: patientID XDS Folder Attribute: codeList |
The codeList shall contain all purpose codes as assigned to the ECR that is to be closed |
| consentInfo | XDS Document | |
| consentDoc (optional) | XDS Document | Scaned documents SHALL be provided acc. to the XDS SD Integration Profile. |
Following this, implementations SHALL satisfy
- the Common constraints on ITI-41,
- the distinct set of constraints which trigger this binding, given in the table below (R = required, O = optional, - = forbidden).
| Constraints | closeECR binding |
|---|---|
| One XDS Document is a consentInfo which gives a new consent or does not revoke all active consents | - |
| One XDS Document is a consentInfo, which revokes all active consents | R |
| The provided XDS Folder and a registered XDS Folder have the XDSFolder.codeList and XDSFolder.patientID in common (i.e. the EFA exists) | R |
| The XDS Folder is not registered (uniqueID) | O |
| The XDSFolder is registered (uniqueID) | O |
Expected Actions
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.04.02}
The XDS Document Repository provider SHALL respond to an ProvideAndRegisterDocument request message with the ProvideAndRegisterDocument response message containing a success indicator.
The provider of the XDS Document Repository MUST verify that the requesting service user has sufficient rights to close an ECR at this ECR Provider. This includes that the service user is registered with the provider and familiar with using ECRs. Additionaly the ECR provider SHALL verify the completeness and consistency of the provided consentInfo document.
In processing this request the ECR Provider SHALL
- assess the access control policy of that ECR with the "modify consent" operation. If this access is denied an error status SHALL be returned.
- setup a folder as specified in the request message
- store the provided documents within the XDR Document Repository
- forward the metadata of the received documents to the XDS Document Registry for registration
- change the status of the ECR and all its partitions (folders) to "grace"
- Adapt all permissions to the new status of the ECR
In case of an error that relates to the transmission of the request or the processing of the EFA security token, the EFA Resource Manager Service provider MUST respond with the respective error status.
Response Message (Full Success Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.04.03}
If the EFA Document Registry Service provider is able to decode the received message and to properly change the status of the ECR and its partitions it responds with an ebXML Registry Response with its status set to "urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Success"
If the service provider wants to respond with further information on the processing of the transmitted data or with a non-critical warning it SHOULD include an additional <RegistryErrorList> element. The severity MUST be set to “urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Warning”.
The following warning messages and codes are defined:
| Condition and Severity | Message | Code | Action to be taken |
|---|---|---|---|
| Request was received but not processed; e.g. because a manual intervention by the ECR provider is required to close an ECR | Processing deferred | 2201 | None |
Response Message (Failure or Partial Failure Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.04.04}
If the XDS Document Repository is able to decode the received message but the processing of the request failed, it responds with an ebXML Registry Response that contains a respective status indicator (see below).The response MUST contain a RegistryErrorList element that indicates the failure condition.
The shutdown of an ECR is an All-or-Nothing operation. Therefore in any case of failure the response status MUST be set to “urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Failure”.
The severity of each registry error message MUST be set to ”urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Error”. Multiple registry error messages MAY be included within a single <rs:RegistryErrorList> element. Apart from the XDS-b error messages defined in Table 4.1-11 of [IHE ITI TF-3] the following error codes are defined for EFA:
| Condition and Severity | Location | Message | Code | Action to be taken |
|---|---|---|---|---|
| The EFA provider requests a higher authentication trust level than assigned to the HP (e.g. password-based login is not accepted for the requested operation). (ERROR) | - | Weak Authentication | 4702 | If possible, the HP SHOULD log in again with a stronger mechansims (e.g. smartcard) and re-issue the request with the respective identity assertion. |
| The ECR provider only accepts consentInfo documents if they are digitally signed by an HP. (ERROR) | OID of the consentInfo document | No Signature | 4704 | If possible, the EFA Client SHOULD re-issue the request with the data signed by an HP. |
| The requestor has not sufficient permission to perform the requested operation (ERROR) | - | No Consent | 4701 | The request MUST NOT be processed by the service provider. The HP MAY request the patient to extend the consent. |
| An ECR of the given purpose does not exist for the patient (ERROR) | - | Policy Violation | 4109 | The request MUST NOT be processed by the service provider. |
Security Considerations
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.04.05}
Message Protection
See Message Protection topic in createECR section.
Audit Trail
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.04.05.02}
Service consumer and service provider actors SHALL write an audit trail according to the EFAv2 Audit Trail Binding.
EFA XDS Binding: listPartitions
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.05}
ECR partitions are bound as XDS folders. Therefore listing partitions corresponds to listing accessible folders which
- are assigned to a given patient, and
- are ECR-classified, and
- are classified with the given purpose.
This EFA binding introduces the following extensions and restrictions on the IHE XDS actor and transaction definitions in order to properly cover the EFA listPartitions operation and to align with the EFA security framework:
- The query is restricted to folder metadata and does not return any data contained within that folders.
- Additional error messages are defined that cover specific failure conditions of the EFA use cases
- The availability of data fields is aligned to EFA privacy requirements
- The application of security measures and the contents of the SOAP security header are specified normatively
Constraints on the Request Message
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.05.01}
The listPartitions request message implements the FindFolder flavor of the IHE Registry Stored Query transaction (ITI-18) request message as defined in [IHE ITI TF-2b#3.18.4.1.2.3.7.3].
The following table shows how the listPartitions SFM is mapped onto the ITI-18 transaction's query arguments:
| listPartitions | ITI-18 | Constraints |
|---|---|---|
| context | SAML Identity Assertion within the SOAP Security Header | see IHE Cookbook |
| patientID | $XDSFolderPatientId | The patient ID used must be resolvable by the ECR Provider. |
| purpose | $XDSFolderCodeList | The codeList MUST contain the ECR-Folder classification code (see EFA XDS Folder Metadata Binding for the respective code). The codeList MUST contain a purpose code, which restricts the query to the partitons of a specific ECR. |
In addition the following constrains must be considered:
- The $XDSFolderLastUpdateTimeFrom and/or $XDSFolderLastUpdateTimeTo query arguments MAY be used. If given, they MUST be considered by the Document Registry.
- The $XDSFolderStatus query arguent SHALL be set to "Approved".
Example
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.05.01.01}
<query:AdhocQueryRequest xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="urn:oasis:names:tc:ebxml-regrep:xsd:query:3.0 ../schemas/query.xsd"
xmlns:query="urn:oasis:names:tc:ebxml-regrep:xsd:query:3.0"
xmlns:rs="urn:oasis:names:tc:ebxml-regrep:xsd:rs:3.0"
xmlns:rim="urn:oasis:names:tc:ebxml-regrep:xsd:rim:3.0">
<query:ResponseOption returnComposedObjects="true" returnType="LeafClass"/>
<rim:AdhocQuery id="urn:uuid:958f3006-baad-4929-a4de-ff1114824431">
<rim:Slot name="$XDSFolderPatientId">
<rim:ValueList>
<rim:Value>'90378912821^^^&amp1.3.6.1.4.1.21367.2005.3.7&ampISO'</rim:Value>
</rim:ValueList>
</rim:Slot>
<rim:Slot name="$XDSFolderStatus">
<rim:ValueList>
<rim:Value>'urn:oasis:names:tc:ebxml-regrep:StatusType:Approved'</rim:Value>
</rim:ValueList>
</rim:Slot>
<rim:Slot name="$XDSFolderCodeList">
<rim:ValueList>
<rim:Value>'ECR^^^IHE-D-Cookbook-FolderClassCode'</rim:Value>
</rim:ValueList>
</rim:Slot>
</rim:AdhocQuery>
</query:AdhocQueryRequest>
Expected Actions
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.05.02}
The XDS Document Registry provider SHALL respond to a Registry Stored Query request message with the Registry Stored Query response message containing a success indicator and listing XDS metadata of all folders that match the given query. The provider of the XDS Document Registry provider MUST verify that the requesting service user has sufficient rights to access the discovered XDS folders.
In processing of this request the ECR Provider SHALL
- assess the access control policy of all folders assigned to the given patient
- discover all folders that match the query and the policy
- respond to the requestor with the metadata of the discovered folders. Metadata provided SHALL comply to the EFA XDS Folder Metadata Binding.
In case of an error that relates to the transmission of the request or the processing of the EFA security token, the XDS Document Registry MUST respond with the respective error status.
Response Message (Full Success Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.05.03}
If the EFA Document Registry Service provider
- is able to decode and process the received message and
- at least one partition exists for the given patient that is accessible to the requestor
it responds with the registry metadata of the discovered partitions.
Response Message (Failure or Partial Failure Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.05.04}
If the XDS Document Registry is unable to successfuly process the query request it MUST respond with a ListResponse message that only contains a <AdhocQueryResponse/RegistryResponse> element.
If no matching folder is discovered or an error occured during the processing of the request, the response status MUST be set to “urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Failure”. If partitons of the patient are discovered but may be incomplete (e.g. due to a not-responding peer in an ECR P2P network), the response status MUST be set to “urn:ihe:iti:2007:ResponseStatusType:PartialSuccess”.
The severity of each registry error message MUST be set to ”urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Error”. Multiple registry error messages MAY be included within a single <rs:RegistryErrorList> element. Apart from the XDS-b error messages defined in Table 4.1-11 of [IHE ITI TF-3] the following error codes are defined for ECR:
| Condition and Severity | Message | Code | Action to be taken |
|---|---|---|---|
| The EFA provider requests a higher authentication trust level than assigned to the HP (e.g. password-based login is not accepted for the requested operation). (ERROR) | Weak Authentication | 4702 | If possible, the HP SHOULD log in again with a stronger mechansims (e.g. smartcard) and re-issue the request with the respective identity assertion. |
| The ECR provider is unable to verify the identity and/or the authenticity of the requestor (ERROR) | Invalid Subject | 4703 | The request MUST NOT be processed by the service provider. |
| The patient is unknown to the ECR provider. | No Data | 1102 | - |
| No partitions are registered for the given patient. | No Data | 1102 | - |
| None of the patient's partitions is accessible to the requestor. | No Data | 1102 | - |
Security Considerations
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.05.05}
Message Protection
See Message Protection topic in createECR section.
Audit Trail
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.05.05.02}
Service consumer and service provider actors SHALL write an audit trail according to the EFAv2 Audit Trail Binding.
EFA XDS/XDR Binding: registerConsent
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.06}
The registration and enforcement of a new patient consent to an existing ECR is performed by placing a consentInfo document that expresses the new consent into one of the ECR's partitions (folders). This may either be a newly created folder of an existing folder that is classified by the ECR purpose codes and as such implicitly represents the ECR that is to be aligned to a new treatment setup.
This EFA binding introduces the following extensions and restrictions on the IHE XDR actor and transaction definitions in order to properly cover the EFA registerConsent operation and to align with the EFA security framework:
- A new folder may be created. Purpose codes shall be provided for the newly created folder as codeList
- A consent information document that expresses the new permissions shall be provided through BPPC. A scanned consent revocation document may be additionaly provided.
- Additional error messages are defined that cover specific failure conditions of the EFA use cases
- The availability of data fields is aligned to EFA privacy requirements
- The application of security measures and the contents of the SOAP security header are specified normatively
Constraints on the Request Message
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.06.01}
The registerConsent request message implements the IHE Provide And Register DocumentSet transaction (ITI-41) request message as profiled in [IHE ITI TF-2b]
The following table shows how the registerConsent SFM is mapped onto the ITI-41 transaction:
| registerConsent | ITI-41 | Constraints |
|---|---|---|
| context | SAML Identity Assertion within the SOAP Security Header | see IHE Cookbook |
| ecrRef | XDS Folder Attribute: patientID XDS Folder Attribute: codeList |
The codeList shall contain all purpose codes as assigned to the ECR that is to be aligned |
| consentInfo | XDS Document | |
| consentDoc (optional) | XDS Document | Scaned documents SHALL be provided acc. to the XDS SD Integration Profile. |
Following this, implementations SHALL satisfy
- the Common constraints on ITI-41,
- the distinct set of constraints which trigger this binding, given in the table below (R = required, O = optional, - = forbidden).
| Constraints | registerConsent binding |
|---|---|
| One XDS Document is a consentInfo which gives a new consent or does not revoke all active consents | R |
| One XDS Document is a consentInfo, which revokes all active consents | - |
| The provided XDS Folder and a registered XDS Folder have the XDSFolder.codeList and XDSFolder.patientID in common (i.e. the EFA exists) | R |
| The XDS Folder is not registered (uniqueID) | O |
| The XDSFolder is registered (uniqueID) | O |
Expected Actions
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.06.02}
The XDS Document Repository provider SHALL respond to an ProvideAndRegisterDocument request message with the ProvideAndRegisterDocument response message containing a success indicator.
The provider of the XDS Document Repository MUST verify that the requesting service user has sufficient rights to register a consent document at this ECR Provider. This includes that the service user is registered with the provider and familiar with using ECRs. Additionaly the ECR provider SHALL verify the completeness and consistency of the provided consentInfo document.
In processing this request the ECR Provider SHALL
- assess the access control policy of that ECR with the "modify consent" operation. If this access is denied an error status SHALL be returned.
- setup a folder as specified in the request message
- store the provided documents within the XDR Document Repository
- forward the metadata of the received documents to the XDS Document Registry for registration
- adapt all permissions that are assigned to the ecrRef to the care team setting as described in the newly provided consent. All previously set permissions must be invalidated.
- if the validity date is changed by the consent: register the new validity with the access control system
- if the purpose is aligned by the new consent: change the eventList codes of all containers that are assigned to the eCR to the new purpose
In case of an error that relates to the transmission of the request or the processing of the EFA security token, the EFA Resource Manager Service provider MUST respond with the respective error status.
Response Message (Full Success Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.06.03}
If the EFA Document Registry Service provider is able to decode the received message and to properly change the settings of the ECR and its partitions it responds with an ebXML Registry Response with its status set to "urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Success"
If the service provider wants to respond with further information on the processing of the transmitted data or with a non-critical warning it SHOULD include an additional <RegistryErrorList> element. The severity MUST be set to “urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Warning”.
The following warning messages and codes are defined:
| Condition and Severity | Message | Code | Action to be taken |
|---|---|---|---|
| Request was received but not processed; e.g. because a manual intervention by the ECR provider is required to change the security settings of an ECR | Processing deferred | 2201 | None |
Response Message (Failure or Partial Failure Scenario)
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.06.04}
If the XDS Document Repository is able to decode the received message but the processing of the request failed, it responds with an ebXML Registry Response that contains a respective status indicator (see below).The response MUST contain a RegistryErrorList element that indicates the failure condition.
The modification of an ECR's security settings is an All-or-Nothing operation. Therefore in any case of failure the response status MUST be set to “urn:oasis:names:tc:ebxml-regrep:ResponseStatusType:Failure”.
The severity of each registry error message MUST be set to ”urn:oasis:names:tc:ebxml-regrep:ErrorSeverityType:Error”. Multiple registry error messages MAY be included within a single <rs:RegistryErrorList> element. Apart from the XDS-b error messages defined in Table 4.1-11 of [IHE ITI TF-3] the following error codes are defined for EFA:
| Condition and Severity | Location | Message | Code | Action to be taken |
|---|---|---|---|---|
| The EFA provider requests a higher authentication trust level than assigned to the HP (e.g. password-based login is not accepted for the requested operation). (ERROR) | - | Weak Authentication | 4702 | If possible, the HP SHOULD log in again with a stronger mechansims (e.g. smartcard) and re-issue the request with the respective identity assertion. |
| The ECR provider only accepts consentInfo documents if they are digitally signed by an HP. (ERROR) | OID of the consentInfo document | No Signature | 4704 | If possible, the EFA Client SHOULD re-issue the request with the data signed by an HP. |
| The requestor has not sufficient permission to perform the requested operation (ERROR) | - | No Consent | 4701 | The request MUST NOT be processed by the service provider. The HP MAY request the patient to extend the consent. |
| An ECR of the given purpose does not exist for the patient (ERROR) | - | Policy Violation | 4109 | The request MUST NOT be processed by the service provider. |
Security Considerations
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.06.05}
Message Protection
See Message Protection topic in createECR section.
Audit Trail
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.06.05.02}
Service consumer and service provider actors SHALL write an audit trail according to the EFAv2 Audit Trail Binding.
EFA IHE-ITI-Binding: listRecordLocations
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.07}
The operation listRecordLocations of the Resource Manager is bound to the transaction Cross Gateway Query [ITI-38] of the XCA profile.
Constraints on the request message
The input of listRecordLocations SHALL be bound to ITI-56 Cross Gateway Query as follows:
| listRecordLocations | ITI-38 Request | Constraints |
|---|---|---|
| context | SAML Identity Assertion within the SOAP Security Header | see IHE Cookbook |
| patientID | $XDSFolderPatientId | The patient-ID SHALL be known by Document Recipient. |
| purpose | $XDSFolderCodeList | The codeList MUST contain the purpose code, which restricts the query to the partitons of a specific ECR. |
Futhermore, the query parameter $XDSFolderCodeList must contain the EFA-MountPoint classification code.
Response Message (Full Success Scenario)
The output of listRecordLocations SHALL be bound to ITI-38 Cross Gateway Query Response as follows:
| listRecordLocations | ITI-38 Response | Constraints |
|---|---|---|
| communityID* | XDSFolder.homeCommunityId attributes | The responder SHALL return the XDSFolder-Elements, that have been registered for this ECR. Each of the XDSFolder-Elements contains a homeCommunityId that identifies the EFA-Provider. |
Response Message (Failure or Partial Failure Scenario)
| Condition and Severity | Location | Message | Code | Action to be taken |
|---|---|---|---|---|
| The cross-community trust has not been established by means of a mutually authenticated channel or message authentication. (ERROR) | - | Policy Violation | 4109 | The request MUST NOT be processed by the Responding Gateway. |
Security Considerations
The request and response messages SHALL be exchanged using a mutually authenticated channel or message authentication.
As for mutually authenticated channels, pairs of EFA-Providers SHOULD negotiate a protocol (f.e. SSH/TSL, VPN, KV-SafeNet) in the scope of contract conclusion.
As for message authentication, the SOAP-Body of the request and response messages SHALL be signed or encrypted using X.509 certificates.
EFA IHE-ITI-Binding: registerRecordLocation
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.08}
The operation registerRecordLocation SHALL be bound to the transaction Provide and Register Document Set ITI-41 [IHE ITI TF-2b#3.41] of the XDR profile.
Constraints on the request message
| registerRecordLocation | ITI-41 | Constraints |
|---|---|---|
| context | SAML Identity Assertion within the SOAP Security Header | see IHE Cookbook |
| patientID | XDSFolder.patientId | The patientId SHALL be know at the target community. |
| purpose | XDSFolder.codeList | The codeList SHALL contain the purpose code. |
| communityID | XDSFolder.homeCommunityId | The homeCommunityId SHALL be the requester's ID. |
Furthermore, XDSFolder.codeList SHALL contain the EFA-classification code and the Mount-Point-classification code. The attribute XDSFolder.sourcePatientId SHALL contain the patientId known in the requester's community.
Expected Actions
| Condition and Severity | Location | Message | Code | Action to be taken |
|---|---|---|---|---|
| The cross-community trust has not been established by means of a mutually authenticated channel or message authentication. (ERROR) | - | Policy Violation | 4109 | The Patient Identifier Cross-reference Manager MUST NOT process the message. |
Security Considerations
The message SHALL be exchanged using a mutually authenticated channel or message authentication.
As for mutually authenticated channels, pairs of EFA-Providers SHOULD negotiate a protocol (f.e. SSH/TSL, VPN, KV-SafeNet) in the scope of contract conclusion.
As for message authentication, the SOAP-Body of the message SHALL be signed or encrypted using X.509 certificates.
EFA IHE-ITI-Binding: notifyOfConsent
Bitte markieren Sie Kommentare zu diesem Abschnitt mit dem Code {EDesa.08}
This binding implements the operation notifyOfConsent of the Resource Manager. It profiles the transaction Document Metadata Notify ITI-53 [IHE ITI Suppl. DSUB].
Constraints on the message
The input of notifyOfConsent SHALL be bound to the Notify Message [IHE ITI TF-2#3.53.4.1] as follows:
| notifyOfConsent | Notify Message | Constraints |
|---|---|---|
| context | SAML Identity Assertion within the SOAP Security Header | see IHE Cookbook |
| patientID | XDSDocumentEntry.patientId | |
| purpose | XDSDocumentEntry.eventCodeList | |
| documentID |
|
Expected Actions
| Condition and Severity | Location | Message | Code | Action to be taken |
|---|---|---|---|---|
| The cross-community trust has not been established by means of a mutually authenticated channel or message authentication. (ERROR) | - | Policy Violation | 4109 | The Document Metadata Notification Recipient MUST NOT process the message. |
Security Considerations
The message SHALL be exchanged using a mutually authenticated channel or message authentication.
As for mutually authenticated channels, pairs of EFA-Providers SHOULD negotiate a protocol (f.e. SSH/TSL, VPN, KV-SafeNet) in the scope of contract conclusion.
As for message authentication, the SOAP-Body of the message SHALL be signed or encrypted using X.509 certificates.